The demand for user privacy and anonymity is at its highest than ever, and appears to be here to stay. In my last blog, I talked about the difference of using VPN and TOR, or VPN over TOR, and vice versa, and we looked at the different use cases for each.
This usage of TOR and VPN typically runs on the host machine, and grants user’s privacy and anonymity, but what about the user’s security? That’s where an anonymity focused OS can also be used to increase the security of the host.
I will be focusing on Tails, Qubes, and Whonix for this blog. There are others such as Kodachi, and Subgraph, which I will briefly touch on.
Tails OS
Goal = Leave no traces.
Tails OS (Debian based) is designed to provide privacy and anonymity; it is the tried and true method of using Live OS on a USB flash drive, which means the OS is installed on separate hardware than the host (your computer), and that all documents and activity live in RAM (volatile memory) which essentially gets deleted once the OS is shutdown or the USB drive is removed, aka amnesiac: forgets about everything that happened.
Data living within volatile memory is not saved anywhere. For example: When you open a word document on your host machine, the document lives in the RAM until you save (write) the document onto a more permanent storage such as HDD or SSD. If you don’t save the document, and you shutdown your host, this document would be lost — RAM is cleared.
You can always create a persistent encrypted partition on the USB drive, which is a supported feature on Tails, that can store your passwords and documents, however you need to make sure this information isn’t highly sensitive.
Tails is a very light OS where it is limited to Tor Internet access, the use of Instant Messenger, and tools to clear metadata.
Tails Pros & Cons:
The following is a short list of pros and cons of using Tails and could help you determine the use case of this fun OS.
Pros:
- Tails is a burn once, use anywhere type of solution. You essentially can use it as a plug-and-go type device as it works on any device with a USB input, and quickly launches. All you have to do it boot into the flash drive.
- It is really easy to setup, and pretty much comes with great out of the box configurations, including Tor configurations
- Tails comes with built-in tools to clean metadata (strip geolocation and other ID tags for increase of privacy on documents)
- Since all the activities are happening on the USB, it essentially protects the host device from malware, or application infections.
Cons:
- Tails does not encrypt documents as default, but does have an encrypted persistent volume feature.
- There is no segregation between activities. Should you have an infected and exploited application, it can affect the rest of the OS. You can easily get around this by unplugging the USB (which kills the OS and dumps the RAM), or re-imaging the entire USB stick.
- Not recommended as a permanent OS as all memory and activities are deleted after shutdown. Also, it is very limited on its capabilities and applications.
Qubes OS
Goal = Virtualization to create isolation.
Qubes is a security-based desktop OS that is best described as a Xen distro (type 1 VM Hypervisor) running virtual Linux domains. It focuses on the user security.
Hypervisor, aka Virtual Machine Monitor (VMM), allows multiple Operating Systems to be executed on the same hardware concurrently. More basically, it allows one host computer to support multiple guest VMs by virtually sharing its resources: memory & processing.
There are 2 different types of Hypervisor:
- Type 1 — Bare metal which resides on the hardware level
- Type 2 — Hosted which resides on the software level.
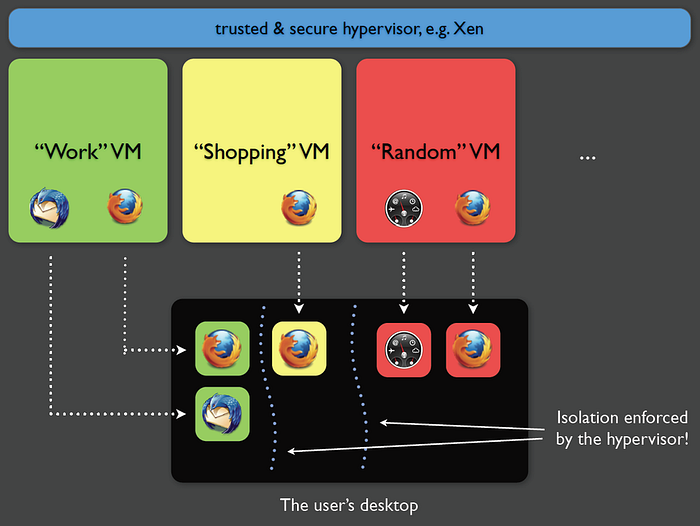
Qubes utilizes type 1 Hypervisor.
The way this works is that Qubes creates separate VMs to use as domains; each app runs on a separate VM and are divided into classes depending on the level of importance. The desktop OS utilizes the hardware of the host computer to virtualize the separate VMs for each separate use.
Qubes Pros & Cons:
The following is a short list of pros and cons of using Qubes and could help you determine the use case of this desktop OS.
Pros:
- Application segregation is strong with this one. Through the use of sandboxed VMs, Qubes ensures that infected/exploited applications can’t affect those within other VMs, or the host.
Cons:
- This OS is not really used for anonymity as its main focus is user security.
- There is no live mode; this only works after an install on the internal host drive.
- On it own, it has great security but poor anonymity — You should consider using Whonix along side.

Whonix
Goal = TorBox
Whonix is a Debian based OS that utilizes a two-part system to establish virtualization to create isolation. The two parts include a Gateway VM and a Workstation VM (both are VirtualBox VMs).
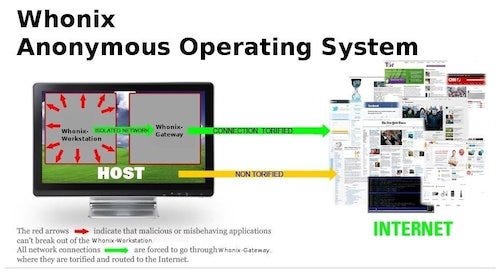
You essentially have two workstations, one (Workstation VM) for privacy and anonymity, and the other (host) for regular browsing. While you are performing activities on the Workstation VM, all your network traffic gets routed through the Gateway VM which is connected to the Tor network. The host has its own internet connection; this ensures stream isolation.
The streams are also “Tor-ified”, which means encrypted via Tor, and protects you from being identified by using Tor circuits for different applications. The level of anonymity of this OS is pretty high, for example:
- The Tor streams make it so it cannot lead to IP address or DNS leaks
- The application being used can only see local IP address
- Timezones cannot be traced
- The clock is set to UTC
- Timestamp HTTP headers get sent to randomly selected web servers.
The Whonix OS can also be combined with a VPN for added privacy.
Whonix Pros & Cons:
The following is a short list of pros and cons of using Whonix and could help you determine the use case of this OS.
Pros:
- High degree of anonymity as that’s its focus for users
- The VirutalBox usage makes it easy for anyone to use
- The default install is simple and requires no extra customization
Cons:
- This is not a portable option
- The only separation is workstation from host — there is no increase of security from risky behaviour. This means that there isn’t much protecting the host from getting infected.
- It is easy to accidentally use the real host when meant to use the workstation VM.
- Using this as a longterm option can cause issues to your host as it uses your host’s hardware for virtualization.
Bonus Option:

Kodachi OS
Goal = Anti-forensic
This is a Debian based Linux OS that provides high level anonymity and security for users accessing the network, plus the added bonus of protecting the system itself.
All the network traffic runs through a VPN and then Tor with DNS encryption (DNScrypt that is installed and configured by default); it removes the possibility of DNS leaks by encrypting requests to OpenDNS.
The OS is built on XFCE (which has a look and feel for a Mac OS) and comes with pre-installed software such as Truecrypt/Veracrypt (encryption), GnuPG, Seahorse (Instant Messenger), and Bleachkit, MAT (Data cleaners).

SubGraph
This is a Linux based OS that is still in its infancy (very new); there isn’t much on it, but I wanted to include it as an option for those who weren’t satisfied with the list of options above. The OS runs custom applications on isolated sandboxes that aid in the protection of the host.
Eeny, Meeny, Miny, Moe
The options given are obviously not the only ones out there, and there is a lot more information on each should you choose to conduct your own research. I feel that it is easier to choose when you know the basics and focus of each so that you can match one to your specific use case. Don’t choose one because your friend told you its the best, do you research and decide for yourself — you have the right to know the wins and the fails of each.